In a recent interview with Bloomberg, Volvo CEO, Hakan Samuelsson said, “It’s our ambition to have a car that can drive fully autonomously on the highway by 2021.” Last year, in an interview with CNBC, Ford Motors CEO, Mark Fields stated that by 2021, Ford’s cars will maintain level 4 autonomy, requiring no steering wheel or gas pedal and that passengers of these cars will “never need to take control of the vehicle in a predefined area.” While this is exciting and marks a milestone on the road to autonomous vehicles, we’re still half a decade or so out before we get to experience the luxury of sitting in the backseat of a self-driving car; leisurely sipping on coffee. In his new post on automotive access control, our CEO, Phil Dumas discusses the opportunities we currently have to create smarter vehicles that can offer us more convenient and intuitive solutions on the way to the actualization of fully autonomous vehicles. To read the article, click here.
It’s hard to believe that it’s almost been two years since UniKey first published this article. Several things in our world have changed since then. Apple has rolled out four new iPhones, Verizon turned on 5G Home, the world’s first 5G network, and there are now more voice assistants like Alexa out there than there are Star Trek remakes (hyperbolic but still, you get the point). Our technology and the consumer products that have stemmed from today’s tech are changing. They’re advancing and progressing into smarter forms of their predecessors and delivering new, intelligent, and exciting experiences. However, no matter the technology advancements that have taken place these past two years, there’s one thing that has remained the same, and that’s the importance of consumer experience.
With CES 2019 currently underway we’re seeing the future arrive in the products companies are debuting at the biggest consumer electronics show in the world. These products are becoming more consumer-centric; delivering more personalized experiences that feel unique to every user. This year’s consumer electronics show exemplifies this movement. With Intellithing’s RoomMe which is the first solution to enable person specific, room-level presence-based operation of IoT smart home devices to Philips introducing a whole host of personalized consumer healthcare products on the showroom floor, personalization is climbing the ranks in importance. While personalization has become a priority for product developers, the key to maintaining consumers’ loyalty still lies in consistency. Jakob Nielsen, dubbed the “King of Usability” by Internet Magazine states that “Consistency is one of the most powerful usability principles: when things always behave the same, users don’t have to worry about what will happen.”
Below is a graphic from retailtouchpoints.com that displays retailer’s continued emphasis and focus on creating a consistent user experience:
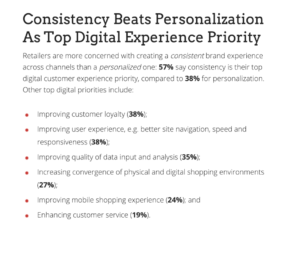
With this insight we can understand that: yes, personalization is becoming an evermore popular element to consumer products/electronics, however, the level of consistency in the products’ quality and reliability will always be the key to a winning experience and happy consumer-base.
At UniKey our top priority is not only keeping customers safe but also providing a consistently reliable at-door experience. To learn more about the platform and surrounding IP that makes this possible, visit unikey.com.
Historically, the physical access control space has been slow to change, as companies took on more of a “wait and see” approach to some of the more innovative pieces of technology being developed. However, in 2018 this mindset seems to have shifted from “wait and see” to “try and see.” What was once something the security enterprise shied away from, is now something that is a must-have. In 2018, more companies began to integrate wireless security systems as well as cloud-based software and smartphone technology as security companies begin to realize the cost-effective and time-saving benefits ingrained in these systems. All of this isn’t news to those of us who are keeping up with the security industry, however, what is new is how the first wave of advanced security systems will impact the security world in 2019. From cybersecurity to data-driven decisions to the convergence of the digital and physical security worlds, here are the top trends we expect to see in 2019:
Cybersecurity
With the growing adoption of new connected security systems, one of the biggest topics of interest we’ll see in 2019 is cybersecurity. According to the Security Industry Association’s (SIA) yearly report, industry leaders envision the upcoming year to be primarily focused on the implementation of robust cybersecurity. One of the greatest motivators of enforcing strong cybersecurity practices is the U.S. Federal Trade Commission’s decision to hold companies accountable for failing to execute standard cybersecurity best practices. With more security systems being housed in the cloud, the call for rigid cybersecurity will be greater than ever.
Data-driven Decisions
With cloud-based and wireless systems we not only have new ways to make physical access control more seamless and intuitive but also new ways to make effective decisions about security. Today we’re living in a time where security needs to be evaluated by something more than what Jacobs and Rudis call, “faith-based security.” Our security systems are growing in complexity and so are the opportunities for data and security breaches. However, with connected security applications, companies are beginning to make better decisions based off pools of actual data, which can facilitate in the establishment of stronger security practices and protocols.
Convergence of the physical and digital worlds
As was mentioned in the above paragraphs, the establishment of cloud-based, wireless systems like mobile access control and other credentialing systems will continue to impact the security industry well into the next year and beyond. With these systems, physical and digital (cyber) security have become codependent on one another. In using these systems we’ll see an overlap in concerns, best practices, as well as the personnel who handle the systems. Karyn Hodgson of SDM magazine writes that “with this change, large enterprise customers are waking up to the idea that not only is their 10- to 15-year-old (or more) access control system probably not secure from a cyber perspective, but that newer systems can offer them so much more return on their investment.” As a result, we’ll see more companies upgrading their legacy security systems to the more robust and innovative security solutions.
Onward to the Next Year
As we make our way into the next year, we envision these security trends maintaining a fair amount of the security industry’s attention. To learn more about the latest in mobile access control or how to better prepare you and your company for the next year, visit unikey.com
Before UniKey’s Executive Vice President, Dr. Tam Hulusi, came to UniKey he worked for several notable companies like Honeywell, Newmark Technology Inc, and HID Global. His leadership experience with these companies gave him an extensive amount of knowledge on the security industry as well as valuable insights on what keeps a company and its employees happy. In his latest article, Dr. Hulusi reflects on the changing work world and how company happiness depends on several important factors and generations of people. Find the article here.




