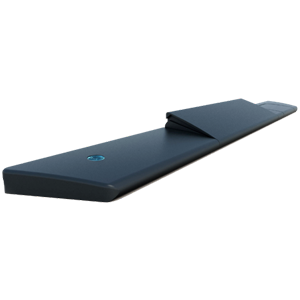
Bridge the Digital and Physical Security Worlds
5+ MILLION
Users Powered By Unikey
+ Access Control Patents
Including Touch-to-Open® Technology
Including Touch-to-Open® Technology
+ Customers Worldwide
7 of Which are #1 in The Market
7 of Which are #1 in The Market




1+
Locks Powered By Unikey
Locks Powered By Unikey












Doors Locked & Unlocked
in Countries Worldwide